GitLab Security Automation: From Pipeline Scanning to Merged Fixes
GitLab put security scanning inside the pipeline. The findings still pile up outside it.
GitLab Ultimate includes an integrated security suite covering SAST, DAST, dependency scanning, container scanning, secret detection, and license compliance. All running inside your CI/CD pipeline, results surfacing in the security dashboard and merge request widgets. For a single-platform DevSecOps strategy, GitLab offers the most complete native security scanning of any Git platform.
Consolidation appeal is real. Organizations juggle an average of 83 different security tools from 29 vendors (Computer Weekly, 2026), and 97% of security leaders are actively consolidating (AI Certs/IDC, 2025). With 4 million unfilled cybersecurity positions globally and over 60% of security analysts reporting burnout, with tool complexity cited as a primary driver (HashiCorp; WebProNews), reducing the number of interfaces your team manages is not a luxury. It is a retention strategy.
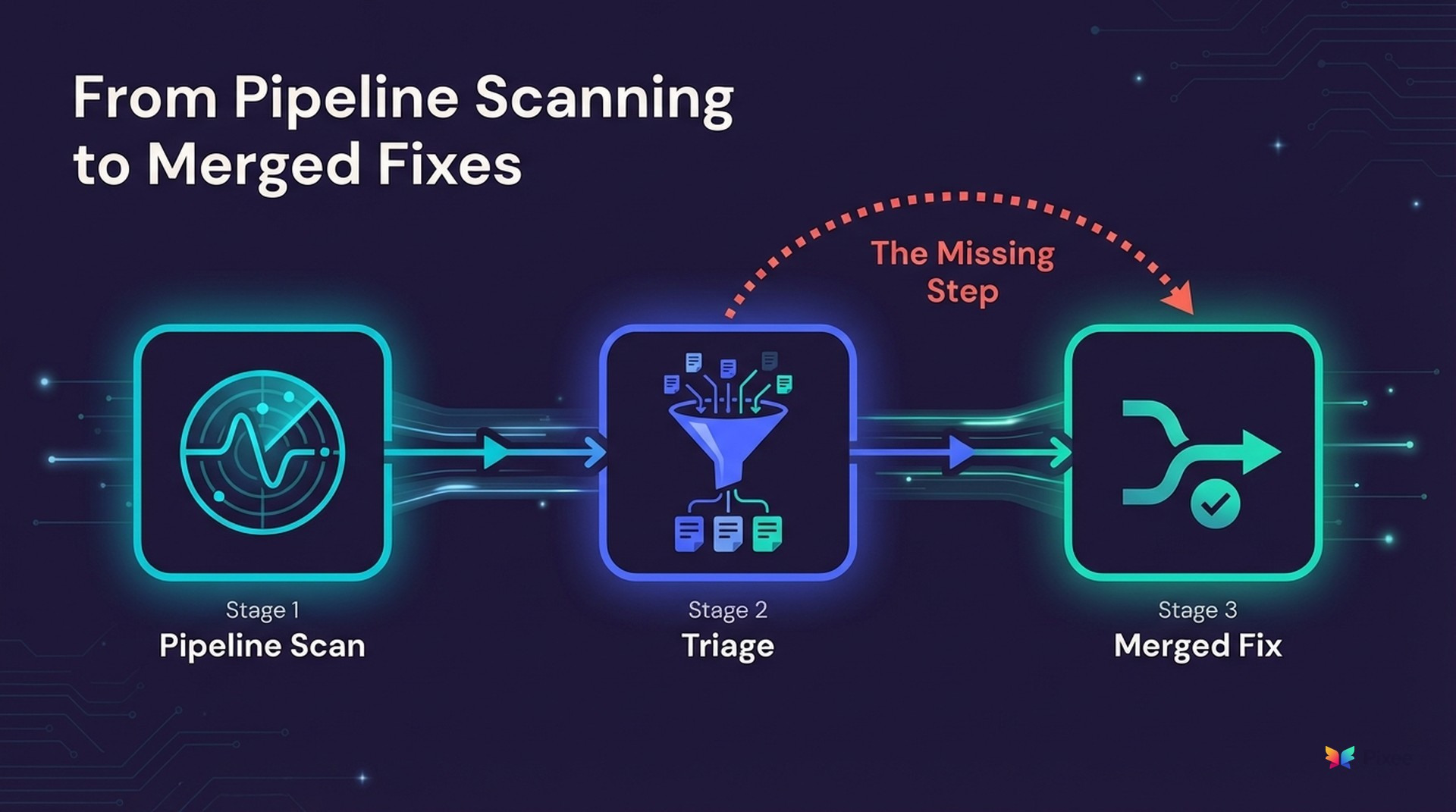
What happens after scanning is the gap. GitLab finds vulnerabilities and presents them in dashboards. Developers see findings in merge requests. But the step between "finding exists" and "finding is fixed in merged code" remains almost entirely manual.
Security dashboards fill with findings. Developers dismiss merge request warnings. Your backlog grows.
This guide covers how to extend GitLab's scanning with automated triage and remediation that turns pipeline findings into merged fixes.
What GitLab's Security Suite Does Well
Integrated Pipeline Scanning
GitLab's security scanners run as CI/CD pipeline jobs. SAST, dependency scanning, container scanning, and secret detection execute automatically on every merge request. No external tool integration required. No separate CI/CD configuration. Scanners ship as part of the platform.
Where it shines. Zero-integration scanning. Security results appear in the same interface developers already use. Security policies can block merge requests with unresolved critical findings.
One constraint worth noting. All security scanning features are locked behind GitLab Ultimate at $99/user/month (Spendflo; eesel.ai). Teams on Premium ($29/user/month) or Free tiers get none of the security scanning, the security dashboard, or the compliance pipeline features. For a 100-person engineering team, that is roughly $87,000 to $100,000 per year after enterprise discounts, before any additional security tooling. As one practitioner observed, "full security features, such as rich DAST and license compliance, sit in Ultimate, not Premium. For many devs, SAST and DAST feel like basic hygiene, not a luxury extra" (eesel.ai).
Security Dashboard
GitLab's vulnerability management dashboard aggregates findings across projects, showing status, severity, and trends. Your security team can triage findings, change status, create issues, and track remediation across the organization from one view.
Strongest for cross-project visibility without tool switching. Built-in workflow for triage-to-issue creation. Policy-driven approval gates on merge requests.
Compliance Framework Integration
GitLab's compliance features (compliance frameworks, audit events, compliance pipelines) connect security scanning to organizational compliance requirements. Security policies can enforce scanning requirements per compliance framework.
Strongest for regulated teams. If you need to demonstrate scanning compliance for SOC 2, ISO 27001, or industry-specific requirements, you can configure enforcement at the group level.
Advanced SAST and Improved Accuracy
GitLab Advanced SAST uses cross-function, cross-file taint analysis to detect complex vulnerabilities with fewer false positives than its earlier Semgrep-based approach. It only reports taint-based vulnerabilities when there is a verifiable flow from source to sink (GitLab Docs). This is genuine progress on detection accuracy, particularly for complex injection vulnerabilities where data flows through multiple functions. For teams relying solely on GitLab's native SAST, Advanced SAST meaningfully reduces noise.
It covers GitLab's own SAST scanner only. Findings from Snyk, Checkmarx, Veracode, or other tools in your stack do not benefit from this analysis. Verifiable taint flow is also not the same as full exploitability analysis. It confirms data reaches a dangerous sink, but does not assess whether security controls along the path would prevent exploitation.
Where GitLab's Security Automation Stops
Findings Without Fixes (and Where Duo Fits)
GitLab's security suite excels at finding vulnerabilities. For most finding types, it does not fix them. When a dependency scan identifies a vulnerable package or a container scan flags an outdated base image, the output is a finding in a dashboard. Converting that finding into a code change, testing it, and getting it merged remains a manual developer task.
GitLab has begun addressing part of this gap. Duo-powered vulnerability resolution (launched as Agentic SAST in GitLab 18.9+) generates merge requests for High and Critical SAST findings, powered by Anthropic's Claude 3.5 Sonnet (GitLab Docs; GitLab Blog). This is a meaningful step forward and worth acknowledging honestly.
Duo's coverage addresses GitLab's own SAST findings only, not dependency scanning, not container scanning, not third-party scanner results from tools like Snyk or Checkmarx. There is no published merge rate or accuracy benchmark for Duo-generated MRs, making it difficult to evaluate production-readiness at scale. Duo is also an additional cost on top of the Ultimate tier.
The dependency scanning gap deserves particular attention. GitLab's dependency scanner identifies a vulnerable transitive dependency and reports the CVE. It does not trace the dependency tree back to the root-level package your code actually imports, analyze whether updating that root package introduces breaking API changes, or generate a merge request with the minimal version bump that resolves the vulnerability chain. When a CVE sits three or four levels deep in your dependency tree, the distance between "finding reported" and "finding fixed" is not a single version bump. It is a dependency chain analysis problem that manual triage handles poorly at scale.
For teams running a single scanner in a single language, Duo may close enough of the gap. For teams running multiple scanners across a diverse stack, the remediation gap remains wide for everything outside GitLab-native SAST.
If your organization uses both Duo-powered vulnerability resolution and Pixee, findings addressed by Duo are automatically excluded from Pixee's queue. No duplicate MRs.
Single-Platform Scanner Scope
GitLab's scanners cover GitLab-hosted repositories. If you also run Snyk for deeper SCA analysis, Checkmarx for enterprise SAST, or Veracode for compliance-driven scanning, those findings exist in separate systems. GitLab's security dashboard does not ingest or display third-party scanner findings in a unified view.
This problem is larger than most teams realize. Even narrowing to application security, enterprises average 5.3 tools per team (Cyentia/RiskRecon). Platform consolidation reduces incident identification time by 74 days and mitigation time by 84 days on average (Security Boulevard, 2025). But consolidation into GitLab's dashboard only works if GitLab is your sole scanner. For most enterprise teams, it is one of several, and the dashboard shows one slice of the total vulnerability picture.
Triage at Scale
GitLab's security dashboard supports manual triage. Developers can mark findings as confirmed, dismissed, or resolved. With hundreds of projects and thousands of findings per pipeline run, manual triage does not scale. When 71-88% of SAST findings are false positives (Ponemon Institute), most of your triage effort goes to noise. Even modern tools show wide variance: Checkmarx scored a 36.3% false positive rate in 2024 Tolly Report benchmark testing (Mobb), and a 2024 SOC survey found roughly 53% of security alerts across tools were false positives (Finite State).
Practical limits emerge at scale. When total vulnerabilities exceed 1,000, the vulnerability report displays "1000+" instead of an exact count (GitLab Docs). Results come from the most recently completed pipeline on the default branch only, not un-merged branches where developers are actively working. Third-party scanner findings cannot be ingested at all. Continuous Vulnerability Scanning can create new vulnerability entries when advisories publish but cannot automatically resolve them when fixes ship (GitLab Docs). For teams with large backlogs across multiple scanners, the dashboard becomes a partial view of a partial picture.
Adding the Resolution Platform to GitLab
Pixee integrates with GitLab CI/CD pipelines and works alongside GitLab's native scanners and any additional tools in your security stack.
Triage Automation
Findings from GitLab SAST, dependency scanning, and any external scanners (Snyk, Checkmarx, Veracode, SonarQube) flow into one exploitability analysis layer. This goes beyond the taint analysis that Advanced SAST performs. Advanced SAST confirms that a data flow path exists from source to sink. Pixee's exploitability analysis also maps your deployed security controls (WAF rules, input validation middleware, auth layers, output encoding) and evaluates whether those controls already prevent exploitation along that path. A SQL injection finding where parameterized queries are enforced by your ORM layer and input validation middleware sits upstream is not the same risk as a SQL injection finding with a raw query and no validation. Both show a taint flow. Only one is exploitable given your actual codebase.
Combined with codebase-aware reachability verification and dependency invocation analysis, this achieves 95% false positive reduction, measured by comparing scanner-reported findings against exploitability-confirmed findings using reachability and control analysis (Pixee Platform Data, 2025).
Instead of manually triaging thousands of findings in the security dashboard, your team reviews a prioritized list of genuinely exploitable vulnerabilities.
Automated Merge Requests
For each confirmed vulnerability, Pixee generates a GitLab merge request. How it generates that MR is where the approach diverges from single-prompt LLM fixes like Duo.
Codebase convention analysis. Before writing any fix, Pixee analyzes your repository's patterns: import styles, error handling conventions, logging frameworks, test structure. A fix for a Spring Boot service using Lombok and SLF4J looks different from a fix for a plain Java service using java.util.logging. Both might address the same CVE. Pixee generates the fix that matches YOUR code, not a generic example that passes compilation but fails code review.
Multi-file reasoning. Duo generates fixes from the context of the flagged file. Pixee traces data flow across multiple files, through middleware chains, across service boundaries. A SQL injection fix in a controller needs to account for the ORM layer, the validation middleware, and the database abstraction. Fixing the controller without understanding the downstream data path produces fixes that either duplicate existing protections or miss the actual injection point.
SCA resolution at the root level. For dependency vulnerabilities, Pixee traces the dependency tree to find the minimum root-level update that resolves the CVE without breaking your direct dependencies. Before generating the MR, it analyzes API surface changes between versions (removed methods, changed signatures, deprecated patterns) and scores breaking change risk at 80-90% confidence. When multiple scanners flag the same transitive dependency differently, Pixee deduplicates across scanners so you fix once, not five times.
Fix verification. Each generated MR includes verification: does the fix compile? Do existing tests pass? Does the fix introduce new issues? Duo generates the MR. Pixee generates, verifies, and explains.
A 76% merge rate (PRs merged without modification within 72 hours of opening, measured across 100,000+ PRs from enterprise deployments; Pixee Platform Data, 2025) reflects fixes that pass developer review, not suggestions that create rework.
Multi-Scanner Consolidation
Bundled-versus-best-of-breed is a real debate, and honest practitioners land on both sides. As Aikido notes, "the depth of each integrated scanner in all-in-one platforms may not always match dedicated tools." Spacelift puts it directly: "DevSecOps isn't achieved with a single tool, but by choosing the right tools that fit your organization's needs."
Most enterprises land in a hybrid model. GitLab serves as the platform backbone for CI/CD and baseline security scanning, supplemented by specialized tools for deeper analysis. Whether your GitLab pipeline runs native SAST plus Snyk for SCA plus Checkmarx for compliance, Pixee provides one triage and remediation layer across all of them. One queue. One workflow. One set of merge requests. Not replacing GitLab's scanning, but closing the gap between scanning and resolution across every scanner you run.
GitLab's Track Record
Enterprises like T-Mobile (40% reduction in CI/CD security incidents) and Siemens (30% faster security threat detection) have adopted GitLab's integrated security features to meaningful effect (GitLab Customers). These results reflect GitLab's native platform capabilities, not third-party integrations. GitLab is a serious security platform. For many teams, the scanning is good enough. What remains unresolved is what happens after scanning.
GitLab Native vs GitLab + Pixee
| Capability | GitLab Ultimate Native | GitLab + Pixee |
|---|---|---|
| SAST scanning | Included (pipeline job) + Advanced SAST taint analysis | GitLab scans, Pixee triages + fixes |
| Dependency scanning | Included (pipeline job) | GitLab scans, Pixee resolves at root level |
| Container scanning | Included | GitLab scans (Pixee does not fix container findings) |
| Automated fix generation | Duo: SAST High/Critical only, no published merge rate | Context-aware MRs across all finding types, 76% merge rate across 100K+ MRs |
| False positive reduction | Advanced SAST taint analysis (GitLab SAST only) | 95% automated reduction across all connected scanners |
| Multi-scanner support | GitLab scanners only | 10+ scanners unified |
| Triage automation | Manual status changes | Exploitability analysis with documented rationale |
| SCA resolution | Flags vulnerable dependency with CVE | Root-level dependency resolution with breaking change analysis |
| Fix approach | Duo: Single-prompt LLM (SAST only) | Multi-step agentic analysis across codebase with fix verification |
| Convention matching | Duo: Generic fix patterns | Codebase-specific conventions (imports, error handling, logging, tests) |
| Breaking change detection | Basic CI pipeline checks | 80-90% confidence scoring with API surface change analysis |
| Dashboard scale | 1,000+ count cap, default branch only | Unified view across all scanners, no count limits |
GitLab's scanning is the foundation. Pixee adds the resolution layer.
Implementation: GitLab + Pixee
Step 1: Connect your GitLab instance to Pixee. Native integration via GitLab CI/CD pipeline job or webhook.
Step 2: GitLab's scanners (and any additional scanners) continue running in your pipeline. Findings flow to Pixee automatically.
Step 3: Pixee triages all findings through exploitability analysis. False positives eliminated. Genuine vulnerabilities prioritized.
Step 4: Pixee generates merge requests against your GitLab repositories. Developers review in the familiar MR interface.
Step 5: Developers merge. Findings auto-resolve in GitLab's security dashboard.
Start with a single project. Run Pixee alongside GitLab's native scanning for one sprint and compare the fix output.
On the economics, Forrester's Total Economic Impact study of GitLab Ultimate found a composite organization realizing $90 million in benefits over three years against $15.4 million in costs, a 483% ROI (Forrester TEI, GitLab-commissioned). Those numbers reflect the full platform value, including CI/CD productivity. Security-specific value compounds when scanning produces fixes, not just findings. Adding a resolution layer on top of GitLab's consolidation closes the loop from scanning through triage through remediation.
Where This Approach Has Limits
- Pixee does not replace GitLab's scanning. It requires scanners to generate findings first. If your scanning coverage has gaps, automated remediation inherits those gaps.
- Merge rates may differ in environments with strict approval policies or protected branch rules. The 76% merge rate reflects commercial enterprise deployments. Organizations with multi-reviewer MR requirements, mandatory security sign-offs, or protected branch configurations may see different numbers.
- Findings requiring architectural changes or cross-service refactoring are flagged for human review rather than auto-fixed. Automated remediation handles well-understood vulnerability patterns. Multi-service architectural issues, business logic flaws, and changes that affect system design require developer judgment.
- Container scanning findings are not remediated. Pixee triages and fixes SAST and SCA findings. Container image vulnerabilities identified by GitLab's container scanner are surfaced but require separate remediation workflows.
See It Working With Your GitLab Projects
Book a demo with your actual GitLab projects. We will show Pixee triaging and fixing findings from your GitLab pipeline and any additional scanners you run.
Related Reading:

