88% of SCA alerts aren't exploitable. We find the 12% that are.
Triage + remediation for your existing scanners. Value in days, not months.
Works with 10+ native scanner integrations, plus any SARIF-compatible tool.
Trusted by enterprise security teams










77% of your application isn't code you wrote. You're responsible for 100% of the breaches.
30% of breaches now involve third-party software. Your tools find thousands of CVEs. Most aren't exploitable. Backlogs grow while real risks wait. Meanwhile, time-to-exploit has collapsed — attackers move faster than manual triage can keep up.
From 10,000 alerts to 847 validated risks. Automatically.
Reachability analysis has limits. Pixee goes deeper.
AI agents research exploitability
Deep Research Agents analyze CVE changelogs, test cases, and security blogs to identify exploitable patterns — not generic severity scores.
Coding agents review YOUR codebase
Armed with research, Coding Agents review your code for those specific patterns. Automated security code review, not just path tracing.
5 minutes, not 6 hours
Full context on every finding: exploit paths, exploitability classification, remediation guidance. Defensible triage automation decisions.
Fixes developers actually merge
Context-aware fixes — dependency upgrades tested for breaking changes, automated PRs matching your code conventions. Developers review every PR before merge. 76% merge rate across 100,000+ pull requests.
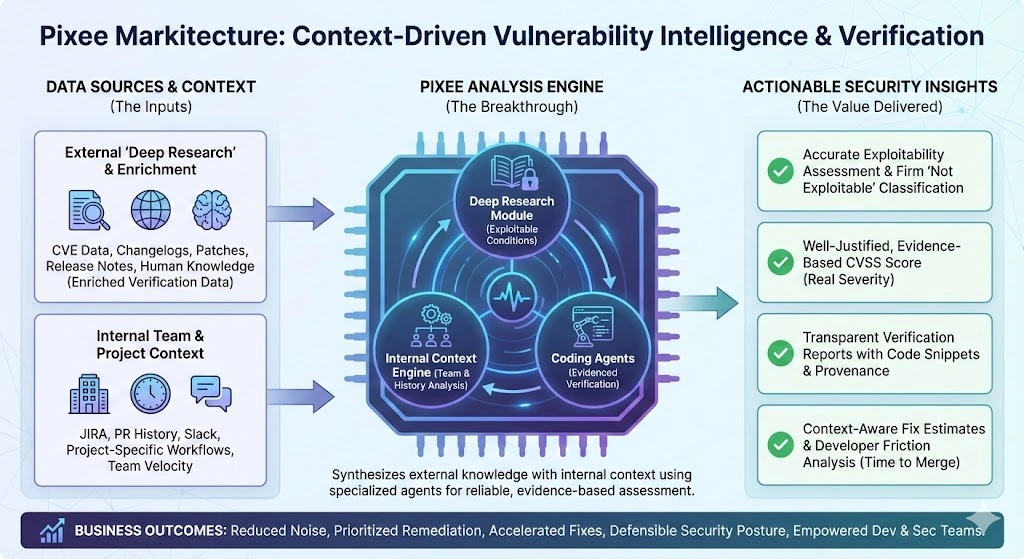
Pixee sits between your scanners and your security workflow. Deep Research Agents analyze external CVE sources while Coding Agents review your codebase for exploitable patterns. The result: validated exploitability assessments, not generic severity scores. Read the complete guide to software supply chain security →
Security teams trust Pixee to cut through the noise
“We went from 10,000 alerts to 847 actionable findings. Our team finally has time for strategic work.”
Head of AppSec, Financial Services
“Pixee validated our existing scanner investment. We added exploitability verification without ripping anything out.”
Director of Security Engineering, Technology
“The 91% reduction in triage time isn't marketing — that's what we measured in our first month.”
VP of Engineering, Healthcare
“We were drowning in alerts. Pixee showed us which 12% actually mattered.”
Security Engineer, SaaS
Ready to cut through the SCA noise?
See how Pixee transforms 10,000 alerts into a prioritized, verified risk list — with evidence you can defend.
Schedule a Demo →Extend your existing scanners. Value in days, not 6 months.
Legacy SCA tools find vulnerabilities. They just can't tell you which ones matter. Add exploitability verification to your current stack — no rip-and-replace required.
Keep your scanners
10+ native scanner integrations, plus any SARIF-compatible tool. No rip-and-replace.
Deploy in days
Self-hosted or cloud. SOC 2 compliant. Air-gapped options available.
Immediate ROI
95% false positive elimination from day one.
Cut triage time by 91%: from 6 hours to 5 minutes per vulnerability
Works with your existing stack
Your Scanner
Any SCA tool via SARIF
Snyk, Dependabot, Mend, Sonatype, Checkmarx, and more. 10+ native integrations.
CI/CD Platforms
GitHub, GitLab, Bitbucket, Azure DevOps
Automated PRs in your existing workflow. No new tools to learn.
Deployment
Cloud, self-hosted, or air-gapped
SOC 2 compliant. Deploy wherever your security requirements demand.
See how Pixee compares:
Enterprise-ready from day one
Type II Certified
Enterprise-grade security controls with annual third-party audits.
Bring Your Own Model
Use your Azure OpenAI or AWS Bedrock. Code never leaves your environment.
Full Isolation
Complete on-premises deployment for regulated industries and sensitive codebases.
