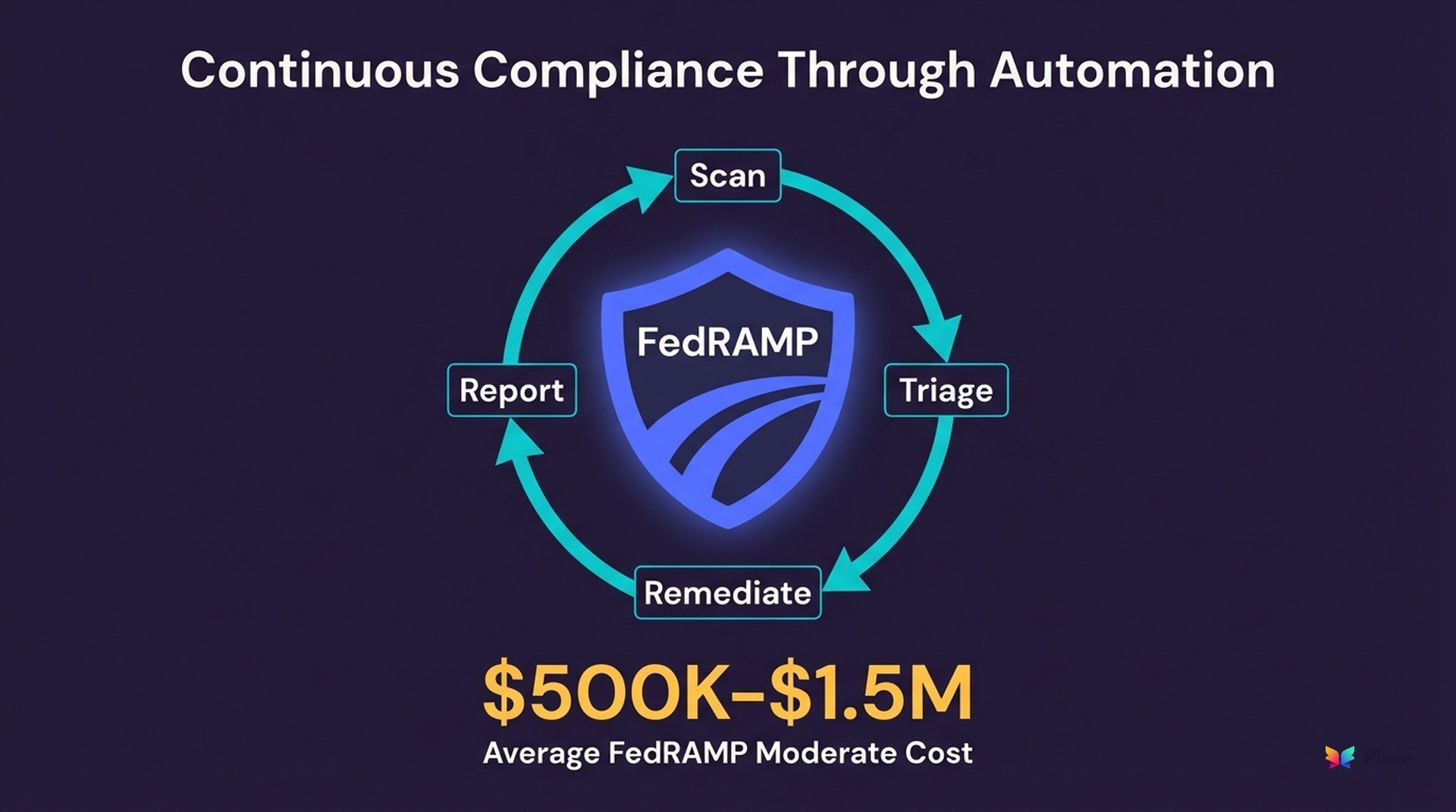
FedRAMP Security Automation: Continuous Compliance Through Automated Remediation
Federal agencies and their cloud service providers face an uncomfortable truth about FedRAMP. Earning an Authority to Operate is the easy part. Keeping it is where most organizations struggle.
FedRAMP Moderate authorization costs $500K-$1.5M and takes 12-18 months (Paramify, 2026; Secureframe, 2026). Moderate baselines cover 323 NIST 800-53 Rev 5 controls plus 17 FedRAMP-specific additions. After more than a decade, only roughly 400 cloud services have earned authorization while thousands remain in use without it. That investment is worth protecting.
FedRAMP's continuous monitoring program demands ongoing vulnerability remediation against strict timelines. High-severity findings require resolution within 30 days, moderate within 90, and low within 180. Miss those windows and your ATO is at risk. FedRAMP will not issue the "FedRAMP Authorized" designation if open High-severity findings exist, and late POA&Ms trigger a formal review of the CSP's authorization (FedRAMP POA&M Playbook). Missing remediation windows is a direct threat to your market access.
For organizations managing thousands of findings across dozens of repositories, manual remediation workflows crack under that pressure.
What Continuous Monitoring Actually Demands
FedRAMP Rev 5, aligned with NIST SP 800-53, establishes continuous monitoring as a non-negotiable requirement for cloud service providers operating in federal environments. The framework goes beyond annual assessments. It requires ongoing evidence that vulnerabilities are identified, prioritized, and resolved within defined timeframes.
Three NIST controls define the scan-fix-verify cycle that FedRAMP enforces.
RA-5 (Vulnerability Monitoring and Scanning) mandates monthly authenticated scanning of all operating systems, web applications, and databases, with reports sent to reviewers monthly.
SI-2 (Flaw Remediation) requires that identified software and hardware flaws be promptly corrected, minimizing the window of exposure.
CA-2 (Control Assessments) ties scanning and remediation together into the audit evidence chain that assessors verify.
In practice, this creates three operational burdens for security teams:
Triage at speed. Your scanners will flag thousands of findings per month. Most are false positives or unexploitable in your specific deployment context. But you need documented evidence for why each finding was dispositioned, not just that it was dismissed.
Remediation with proof. Auditors want to see that real vulnerabilities were fixed, when they were fixed, and that fixes were verified. A closed Jira ticket does not constitute audit-ready evidence. Code changes with security context do.
Continuous reporting. Monthly ConMon reporting requires submitting vulnerability scans, an updated POA&M, current system inventory, and documented deviation requests to the authorizing agency or FedRAMP PMO. Organizations report spending weeks manually reconciling security posture across these deliverables (Wiz, 2025; Vanta, 2025). Both the GRC team managing the POA&M and engineering service owners responsible for patching must stay synchronized. Manual tracking in spreadsheets becomes untenable past a few hundred findings.
Where Manual Remediation Breaks Down
Government-adjacent security teams often operate with smaller headcounts than their private-sector counterparts. A team of 3-5 security engineers supporting a FedRAMP-authorized product might manage 50+ repositories. At an industry average of 581 vulnerabilities per codebase (Black Duck, 2026), the math works against them immediately.
For cloud-native architectures, FedRAMP's container scanning requirements add another constraint. Only containers from images scanned within a 30-day window can be deployed in production, and the container registry must be monitored per unique image (FedRAMP Container Scanning Requirements). For teams managing hundreds of container images across microservices, this creates a scan-before-deploy gate that manual processes cannot maintain at velocity.
Manual triage and remediation also introduces inconsistency. When different engineers disposition the same finding type differently across repositories, auditors notice. Inconsistent triage rationale is a finding in itself during FedRAMP assessments.
High-severity remediation windows are particularly unforgiving. When a critical CVE drops and affects multiple services, security teams scramble to coordinate fixes across repositories while maintaining their regular triage workload. According to Google's Cybersecurity & Threat Research report (2026), the window from CVE disclosure to mass exploitation has compressed to 48 hours. The 30-day remediation deadline is a compliance floor, not a security ceiling.
How Automated Triage and Remediation Supports FedRAMP
Automated vulnerability management addresses each of these failure modes by producing consistent triage decisions, auditable fix records, and faster remediation cycles.
Triage Automation for Consistent Dispositioning
Automated triage evaluates every finding against your actual codebase context. Rather than reviewing thousands of alerts manually, exploitability analysis determines which findings are reachable and exploitable in your specific deployment. Findings that cannot be triggered in production are documented with evidence-backed rationale, exactly the kind of documentation FedRAMP assessors expect.
This eliminates the inconsistency problem. Every finding of the same type receives the same evaluation methodology, producing uniform evidence across repositories.
Automated Remediation for Auditable Fix Records
When automated systems generate pull requests to resolve confirmed vulnerabilities, each PR carries security context explaining what was found, why it matters, and what the fix changes. These PRs create a built-in audit trail: timestamped code changes, review approvals, merge records, and time-to-fix measurements.
For FedRAMP reporting, this evidence chain maps directly to what assessors verify during continuous monitoring reviews. Instead of reconstructing remediation history from ticket systems and git logs, the evidence exists as a natural artifact of the fix process.
Reporting-Ready Metrics
Automated remediation produces the data FedRAMP reporting requires without manual collection. Mean time to remediation, findings by severity over time, and remediation rates by category all emerge from the workflow itself rather than from someone compiling spreadsheets before each POA&M submission.
Deployment Flexibility for Federal Requirements
Federal environments impose strict data residency and handling requirements. Code from government systems cannot transit through third-party cloud infrastructure without careful authorization.
Pixee supports self-hosted and VPC deployment models where your source code never leaves your infrastructure. This deployment flexibility means government cloud service providers can adopt automated triage and remediation without introducing new data residency risks into their authorization boundary.
For air-gapped and IL4+ environments, Pixee supports self-hosted deployment within your authorization boundary. The core analysis engine (reachability analysis, control detection, and fix generation for dependency updates and common vulnerability patterns) operates without external connectivity.
AI-assisted fixes for complex patterns require a self-hosted LLM (supported models include open-weight options deployable on government cloud infrastructure). Organizations should evaluate the accuracy trade-off. Self-hosted models handle ~80% of fix patterns with comparable quality, while the remaining 20% (complex refactoring, novel vulnerability types) may require cloud-connected models or manual remediation.
Pixee is not itself FedRAMP authorized. For CSPs adding Pixee to their authorization boundary, the self-hosted deployment model means Pixee operates as a development tool within your existing boundary rather than introducing a new external service dependency.
Implementation Path for FedRAMP Environments
Organizations pursuing FedRAMP security automation typically follow a phased approach.
Phase 1. Visibility. Connect scanners to a unified triage layer. Most FedRAMP-authorized products already run multiple scanning tools. Consolidating their output into a single view with automated exploitability analysis immediately reduces triage burden and produces consistent dispositioning evidence.
Phase 2. Automated remediation on confirmed findings. Begin with dependency updates (SCA findings), which represent the highest volume of FedRAMP-relevant vulnerabilities and carry the lowest risk of behavioral changes. Automated PRs for dependency bumps often achieve merge rates above 76%, defined as PRs merged without modification within 72 hours of opening, measured across 100,000+ PRs from enterprise deployments (Pixee Platform Data, 2025). Government codebases with stricter change management processes may see different merge rates; the 76% figure reflects commercial enterprise deployments.
Phase 3. Expand to SAST findings and custom code. Once the team trusts automated remediation for dependency updates, extend to static analysis findings in application code. This covers injection vulnerabilities, insecure configurations, and other SAST categories that FedRAMP assessors specifically examine.
Phase 4. Continuous monitoring integration. Feed remediation metrics into your continuous monitoring reports. Automated time-to-fix data maps directly to FedRAMP POA&M requirements, reducing the manual reporting burden that typically consumes 1-2 days per monthly cycle.
FedRAMP Itself Is Moving Toward Automation
The FedRAMP 20x initiative, launched in March 2025, explicitly replaces manual document reviews with automation and standardized data structures. Phase 1 (the Low pilot) completed in September 2025 with 12 authorizations, some granted in under two months compared to the traditional 12-18 month timeline (FedRAMP.gov). Phase 2, targeting Moderate baselines with roughly 13 participants, introduces an overhauled Vulnerability Detection and Response standard alongside Key Security Indicators (KSIs) that replace manual document reviews.
This trajectory confirms that FedRAMP itself is moving toward automation-first compliance. CSPs that automate triage and remediation now are building the infrastructure the program will increasingly require.
Two additional terminology changes reflect this shift. "FedRAMP Certification" is replacing "FedRAMP Authorization" to avoid confusion with agency ATOs. And impact levels are transitioning to "Certification Classes": Class B (Low/Li-SaaS), Class C (Moderate), and Class D (High), with Consolidated Rules for 2026 (CR26) applying to all CSPs by December 31, 2026 (Ignyte, 2026; Elevate Consult, 2026).
A caveat on 20x: all planned phases have been delayed approximately three months, and the shift from document-based review to automation-based KSIs is unproven at scale. Whether the program delivers on its timeline remains to be seen. But the direction is clear: more automation, less manual review. That direction favors CSPs that have already automated their vulnerability management workflows.
Why Automation Fits the Compliance Model
FedRAMP continuous monitoring was designed for a world where vulnerability management happened manually. Its timelines (30, 90, and 180 days) assume human-speed remediation. Organizations that automate triage and remediation do not just meet those timelines more consistently. They produce better evidence, maintain more uniform processes, and free their security engineers to focus on architecture-level risks that automation cannot address.
One important limitation: automated triage and remediation handles the bulk of scanning findings (dependency updates, known vulnerability patterns, configuration issues) but does not replace human judgment for business logic flaws or novel attack vectors. The goal is to automate the 80% of findings that are well-understood so security engineers can focus their expertise on the 20% that require architectural reasoning.
For cloud service providers maintaining a FedRAMP ATO, the question is whether their current remediation velocity and evidence quality can survive the next assessment. If the honest answer involves spreadsheets and heroics, schedule a technical walkthrough to see how automated triage and remediation map to your continuous monitoring requirements.

